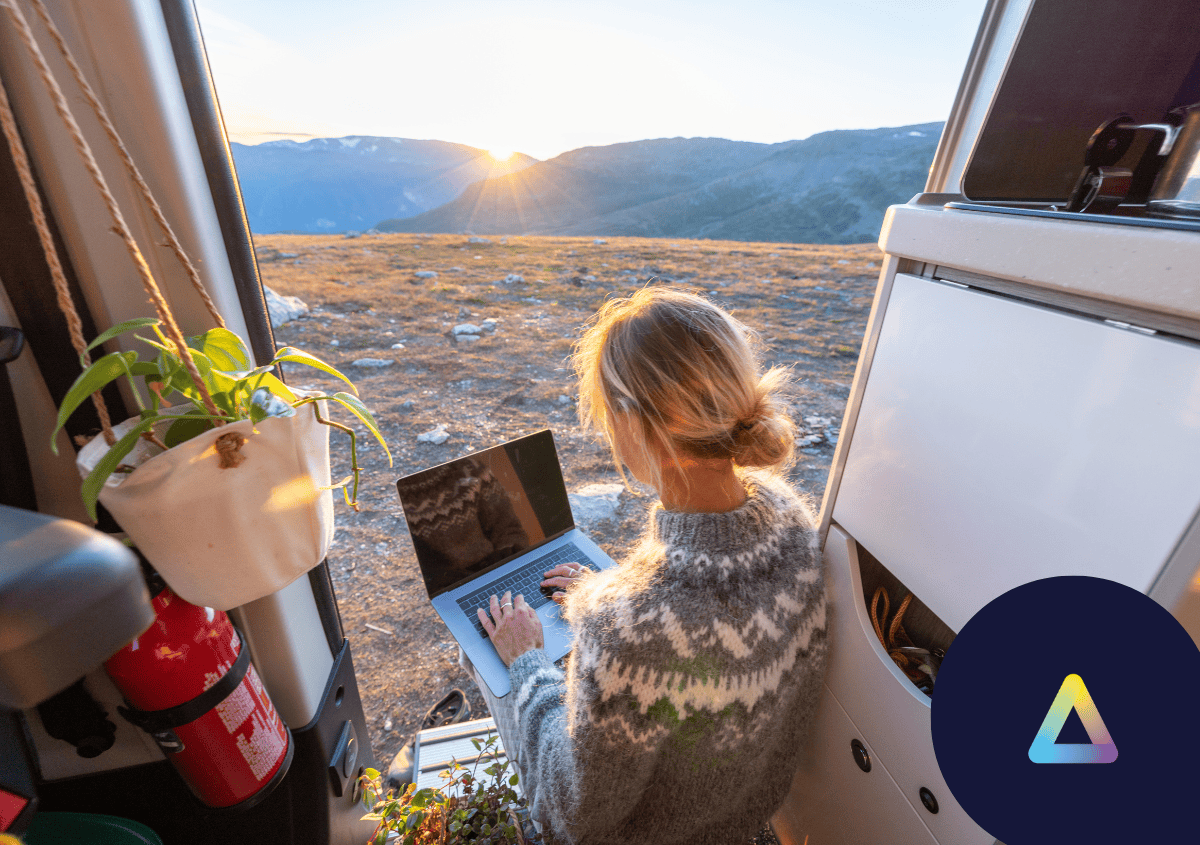
Dispelling the Myths Around Remote Working
Remote work has become a significant trend in recent years, accelerated by global events and technological advancements. Despite its growing popularity, numerous myths and misconceptions still surround the practice. Let’s debunk some of the most common myths about remote work and uncover the reality of this modern work style. Myth 1: Remote Work is not … Read more